- Image via Wikipedia
We try to cover basic security best-practices as much as possible. We talked about the value of NoScript, a Firefox plugin that prevents JavaScript from loading on web pages unless specifically allowed by the user. Today, we’re going to examine why reading email as HTML is a bad practice from a privacy, security and usability standpoint. We’ll also look at how to fix your email client to read all messages as plain text.
HTML stands for Hyper-Text Markup Language and is the foundation of the modern Internet. It is the way web designers can specify that certain text should be linked to other web pages and how images can be displayed on websites.
Email was never intended to be anything other than a messaging system. At some point, email clients began using a browser or browser-like rendering system to display any HTML in emails graphically. As if this wasn’t bad enough from a usability and privacy perspective, it soon followed that they began to interpret scripting as well, thus bringing all of the security dangers of malicious websites to our email boxes.
Privacy
Reading HTML email is bad from a privacy perspective. There’s a great article at About.com by antivirus professional Mary Landesman called Why plain is better. It states the following.
HTML-rendered email can be virtually wiretapped through the use of invisible images, specially formed links, and other techniques that allow email to be tracked. For example, unique serial numbers are often assigned to invisible images stored on a remote server. Each time the email is read, those images are accessed, providing a record of whether the email was opened.
Imagine if each time you checked your post office mail box someone recorded which letters you opened and sent a report back to each sender. It’s amazing that the objections regarding government wiretapping and the privacy of medical records are made by the same people who haven’t secured their inboxes from such observation.
In addition to tracking image loads, many times the links themselves are coded so that the sender can know exactly which link you click. The link connected to the words website.com at the top of the email may be a different link than the word website.com at the bottom of the email.
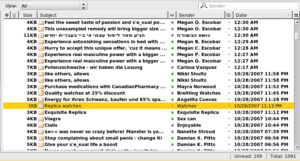
The same tracking systems in HTML used by over-zealous marketers are also used by spammers to tell if inboxes are valid. An email address that consistently loads the HTML-included image means that spam sent to it is being read – or at least opened – and is a much higher-value target than an email address that never loads the image.
Security
Reading HTML email is bad from a security perspective. Phishing is a common practice wherein a user is tricked into providing login credentials, like a username and password, or other sensitive data such as credit card information to a malicious website. One of the many possible baited-hooks used in these attacks is sending an email that looks like an urgent and official email from your bank. The pretty picture says click here to login and takes you to a web page that looks just like your bank’s login page. What you don’t notice is that the URL is slightly different. When you submit the form with your username and password, the malicious page sends your information to the hacker who then can use it to login to your bank’s real website.
Scripting refers to the ability of a program to interpret commands given to it by the content of the document it’s rendering. It’s very common on web pages, but has begun to creep into other types of documents where it doesn’t belong. PDFs, spreadsheets and email are just a few of the types of content that now interpret scripting and now have the associated security issues.
Scripting allows documents to essentially run programs on your computer. Benign scripts may simply ensure that the data you enter into a PDF form is valid, triggering a pop-up if you try to enter a letter into the phone number field. Malicious scripts, however, can be much more pernicious.
Steve Gibson from Gibson Research Center explained one possible scripting use in episode 52 of the Security Now! podcast.
standard JavaScript with no bugs, no exploits, no buffer overruns, no mistakes at all, can be used to port scan your internal network, identify devices, take them over, reprogram them…
Unfortunately, many email clients that render email as HTML allow JavaScript to execute when the document is loaded, so even the simple act of selecting an email with an open preview pane may be enough to cause serious damage.
Even without scripting, email can make use of advanced HTML and CSS techniques to overlay links on parts of the document that don’t look like links so that an accidental click anywhere might send you to a web site in your browser that has the malicious scripts there.
Usability and speed
HTML email is bad from a usability perspective. If you accept that the purpose of email is simply to receive messages, then what faster way to read those messages than in simple text? The different images, font sizes and color choices can take seconds to adapt to, and content in different areas or columns can be difficult to prioritize. This extra time and confusion adds up substantially for those of us with a lot of email to parse and very little time in which to do it.
Benefits of plain text email
Reading email as plain text solves all of the problems listed above.
- Plain text email doesn’t support images, so you can’t be tracked by the email senders
- Plain text email lets you see the links you’re clicking so you can tell if you’re clicking on a link that goes to capitalone.com or one that sends you to capitalone.evilsender.com.ru
- Plain text email doesn’t support scripting so your email doesn’t try to perform actions on your computer
- Plain text email is easier and faster to read
Fix your email reader
In defense of email readers, recent progress has certainly improved the security of clients like Outlook and Thunderbird. While they’re improved, they’re by no means completely secure, as each regularly releases security patches and updates to prevent the latest vulnerabilities.
Even if the browser is completely secure and rendering HTML perfectly, a link on an image or anchor text could still send you to a phishing website. Even if you turn off images and scripting and have the latest and greatest anti-phishing software running on your computer, you’re still left with the annoyance of varying typography and colors that simply aren’t an issue with plain text email.
Outlook
Here’s how to fix Outlook 2003 from the Microsoft support article on the subject.
- Start Outlook 2003.
- On the Tools menu, click Options.
- On the Preferences tab, in the E-mail area, click E-mail Options.
- In the Message handling area, click to select the Read all standard mail in plain text check box.
Here’s how to fix Outlook 2007 from the Microsoft support article on the subject.
- Start Outlook 2007.
- On the Tools menu, click Trust Center, and then click E-mail Security.
- Under Read as Plain Text, click to select the Read all standard mail in plain text check box.
- To include messages that are signed with a digital signature, click to select the Read all digitally signed mail in plain text check box.
Thunderbird
Thunderbird is even easier to secure.
- Start Thunderbird
- On the View menu, click Message Body As and select Plain Text.
Remember that neither modification is permanent. Outlook will tell you that a message has been converted to plain text and if you’ve decided that it’s from a trusted source and for some reason you wish to view it as HTML, you can click the header of the message to do so. All Thunderbird requires is that you simply select view > message body as > original HTML.
HTML is for the web, text is for email. Reading email as simple text is safer, faster and protects your privacy. Soon, we’ll look at this issue from a marketing perspective and learn why sending email as plain text is better for your brand and better for your subscribers and customers.

