Update January 2020
I no longer recommend Private Internet Access due to its recent acquisition.
In this third installment of my series on security, I’m going to explain what a VPN is and why you should use one every time you’re away from the home or office. You might even want to use one at home, too. If you don’t want to read everything here or you don’t feel like you understand it, here’s the take-home message: if you’re away from your home or office, always use a VPN when you connect to the internet. It’s easy and inexpensive.
Why use a VPN?
 I’m sitting in the airport, getting ready to leave for the NAA’s Designation Academy in Las Vegas. I know many other auctioneers from around the country are doing the same thing. I also know that many of them will want to connect to the internet using their phones or computers while they’re away from home. Many, if not most, will do so without using a VPN, putting their accounts and data on their phones and computers at risk.
I’m sitting in the airport, getting ready to leave for the NAA’s Designation Academy in Las Vegas. I know many other auctioneers from around the country are doing the same thing. I also know that many of them will want to connect to the internet using their phones or computers while they’re away from home. Many, if not most, will do so without using a VPN, putting their accounts and data on their phones and computers at risk.
A VPN is a virtual private network. It’s an encrypted, private tunnel between computers over the internet. There are a few different examples for how useful such a private tunnel can be.
Remote access
Imagine a secure company network. Maybe at your office you have a username and password to login while you’re on the network to access your printers and your server or other computers. However, what if you wanted to access your printer or the files on your server while you weren’t at the building? A VPN would let you safely connect to your network at the office from your house or mobile hotspot. This type of VPN would be configured on your network and your computer and wouldn’t require a third party service, so it’s not really the type of VPN we’re interested in today.
Security and privacy
This is the use I’m focused on today. If you connect to public wifi at a coffee shop, hotel or convention center, much of the communication between your computer and the internet is unencrypted, or in the clear. This means anyone with common software can connect to the same network and watch not only what sites you go to but, in some cases, capture your account information.
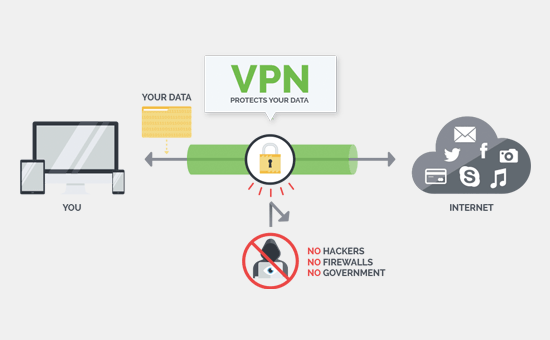
Using a VPN when on public wifi would give you both security and privacy. You would connect to the public wifi, but instead of all your traffic going out on the internet from that location, all your traffic would go through the tunnel to the VPN provider before going out onto the internet. This is essentially a game of keep away from anyone else on that free wifi who would like to get at your data. Here’s a diagram from IPVanish showing how it works.
Bypassing geo fencing
The websites you visit know where you are based on your IP address. If you want to see what those websites can see about you, take a look at infosniper.net. Geofencing is the practice by some streaming services wherein they provide different programming to people in different areas. Netflix, for example, has different content in Canada than they do in the US. ESPN will blackout ballgames for some users based on where they are. Since using a VPN changes your IP address, one common use for VPNs is bypassing this geofencing. Most VPN providers let you select which town or even country you want to appear to come from when using their services.
Using a VPN
It’s true that you could use your own router at home or work to allow you to connect back to your own network from anywhere on the internet to get the same security as one of the paid services, but it’s beyond the scope of this article. I’ll skip discussing the setup and configuration of a roll-your-own VPN setup and look at using a paid service from a VPN provider.
Computer
Your VPN service will have an app for your PC or Mac. When you connect to the public wifi, you simply tell that app to connect to the VPN. You can then browse safely and securely knowing that all your traffic is being transmitted to that VPN provider’s server before it goes out onto the internet.
Phone
Similarly, most VPN providers have apps for Android and iOS that make it just as easy to connect to the VPN. Now that unlimited data plans are becoming ubiquitous, it’s less important to connect to wifi with phones. If you do ever connect your phone to a free wifi network, it’s crucial that you use a VPN.
Selecting a VPN
The first rule when selecting a VPN provider is to never use a free service. There are a few exceptions in the case of reputable VPNs offering a free version that’s slower than using a paid premium account, but the general rule is that if you’re not paying for the VPN then it is making money from you by selling your browsing data.
Most VPNs are really inexpensive. The gold standard is a service called Private Internet Access and it costs under $4 per month if you pay for a couple years at a time. If you’re just wanting something inexpensive to keep you safe while you’re on public wifi, you can also run over to StackSocial and grab one of the lifetime subscriptions to one of the no-name VPNs. They’ll probably do a good job of protecting you from hackers and changing your IP address, but they might not be as reliable at protecting you as PIA if a company or government went to them and asked what you were doing when. A cheaper and less well-known VPN also might go out of business, rendering your lifetime subscription worthless.
If you’re looking for a reputable VPN that offers a free tier to try before you buy, ProXPN is a good option. It’s fast enough to check email and Facebook, but probably not fast enough to stream video.
If you want to learn more about the different VPNs available, TorrentFreak publishes a good question and answer set for myriad VPNs each year. Here’s their 2017 VPN comparison.
Other reasons to use a VPN
Even when you’re at home or using your cell phone’s data or hotspot, your internet provider or cell phone company is tracking your activity. Verizon made news a few years ago when they began adding tracking headers to the traffic of all of their users, allowing websites to track Verizon customers around the web. Users could opt out of this tracking, but I’m guessing a very small percentage of their customers actually did. Some less-than-reputable internet providers also intercept traffic and inject or swap out ads on the pages you visit. Using a VPN would ensure that your traffic isn’t intercepted, monitored or altered by your internet provider.
Downside of a VPN
The only downside of using a VPN, other than the small cost, is speed. Because you’re routing all your traffic through a third-party service, it’s never going to be as fast as directly connecting to the internet. VPN providers are getting better, and reputable VPN services are so fast that the speed difference is usually negligible, but there can be significant differences in performance from one provider to another.
Summary
Don’t connect to the internet away from home without using a VPN. As it looks like we might lose the fight over net neutrality, finding a good and reliable VPN will become an even more imporant part of using the internet safely wherever you are and however you connect.

 Just as
Just as  The screen is a large, 6″ OLED panel that, like other recent phones, is taller than phones of the past. This 18:9 aspect ratio makes it possible to fit a larger screen on a smaller phone. Indeed, the V30 is noticeably smaller than the V20 with a screen that’s significantly bigger. The screen is curved on the edges. I don’t like curved screens, personally, but they’re quite popular and the V30’s makes it feel much thinner than the G6 even though it’s actually slightly thicker.
The screen is a large, 6″ OLED panel that, like other recent phones, is taller than phones of the past. This 18:9 aspect ratio makes it possible to fit a larger screen on a smaller phone. Indeed, the V30 is noticeably smaller than the V20 with a screen that’s significantly bigger. The screen is curved on the edges. I don’t like curved screens, personally, but they’re quite popular and the V30’s makes it feel much thinner than the G6 even though it’s actually slightly thicker.



 Knowing that I was in the middle of fall harvest, Verizon sent me their
Knowing that I was in the middle of fall harvest, Verizon sent me their  LG V30 review summary
LG V30 review summary































 It was 2007. NAA Conference and Show was in San Diego. My bags were packed in my truck. I swung by the office to grab my computer and other electronics that I’d need for the week in California. As I walked out the door for my two hour drive from Manhattan, Kansas, to the Kansas City airport, I realized I’d forgotten something. I sat my computer bag on the ground next to my pickup’s passenger door and went back inside. When I returned, I got in my truck, cranked the wheel to the left and backed out, only to realize that my front tire just rolled over my laptop bag. My computer — and my mood — was crushed. I had unfinished work for upcoming auctions that I’d planned to do on the plane and I had no time before my flight to prep another computer. It made for an interesting and uncomfortable trip.
It was 2007. NAA Conference and Show was in San Diego. My bags were packed in my truck. I swung by the office to grab my computer and other electronics that I’d need for the week in California. As I walked out the door for my two hour drive from Manhattan, Kansas, to the Kansas City airport, I realized I’d forgotten something. I sat my computer bag on the ground next to my pickup’s passenger door and went back inside. When I returned, I got in my truck, cranked the wheel to the left and backed out, only to realize that my front tire just rolled over my laptop bag. My computer — and my mood — was crushed. I had unfinished work for upcoming auctions that I’d planned to do on the plane and I had no time before my flight to prep another computer. It made for an interesting and uncomfortable trip. For many years, the right answer for encryption was a product called TrueCrypt. It was free software and the encryption was bulletproof. A few years ago, the TrueCrypt project closed down. Luckily it’s successor, called
For many years, the right answer for encryption was a product called TrueCrypt. It was free software and the encryption was bulletproof. A few years ago, the TrueCrypt project closed down. Luckily it’s successor, called